Cipher machine
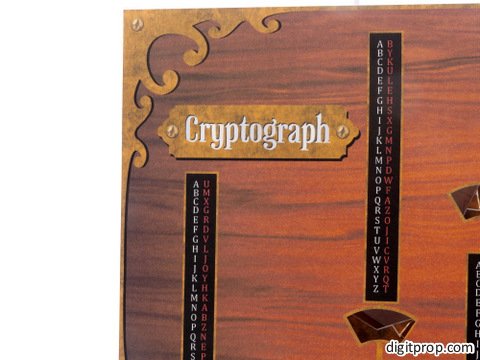
This is something I originally made for the son of a good friend of ours. It’s a cipher machine I call ‘the cryptograph’. I tried to give it a little bit of a steampunk look.
First, some basics about cryptography: If you want to encrypt a text, an easy and obvious approach is a substitution alphabet, where you replace each letter by another letter taken from a table. The drawback in this case is that such a code is easy to break with something called frequency analysis. Since the average frequency of each letter can easily be calculated for any given language, it is easy to guess the substitution code. For instance, the most frequent letter in common English is ‘e’, and therefore the most frequent letter in an encoded message is very likely substituting ‘e’.
For this reason, as an improvement so-called polyalphabetic ciphers were invented. These are schemes where you use multiple different substitution tables. The famous enigma machine, for instance, uses a polyalphabetic cipher.
Now, without the relatively complicated electronics of the enigma, it is a bit difficult to find a reliable scheme for switching between the various substitution tables. This is where the cryoptograph comes in: It indicates which alphabet to use for each consecutive letter of a message.
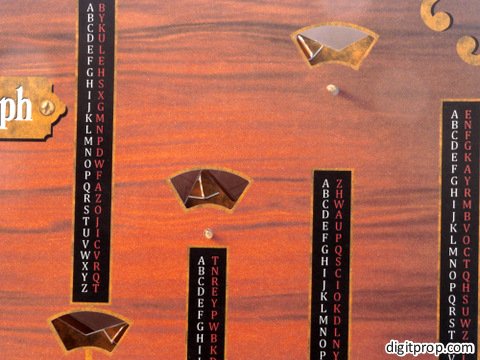
How does it work? You insert a marble at the top, it runs through the machine and emerges in one of five baskets. You then use the substitution table above that basket for the first letter. Then you repeat the process, each time using the table indicated by the marble.
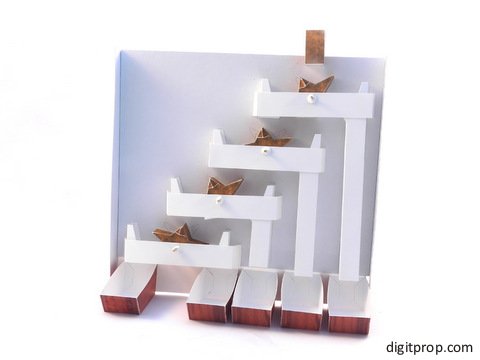
If you remove the cover, this is what the internals look like:
The machine consists of four ‘binary’ switches. Each switch is either in a left or right-facing position, and when a marble runs across a switch, it changes its orientation. The design of the switches is based on this beautiful binary adder on woodgears.ca (a site I highly recommend).
So essentially this is a binary counting mechanism. However, we use it to keep track of which substitution table to use for each letter. Using binary switches means that the rightmost table is used for every second letter. This is of course not extremely secure, and for very long messages it makes the cipher again vulnerable to frequency analysis, but for shorter messages the convolution of the multiple substitution tables is still working just fine. By the way, here is a paper model of the enigma cipher.
Here is a video on how to operate the machine:
Now, how to build the machine: You can download the printable PDF at the bottom of this page.
Start with the back plane and glue it to the sides. It connects with the sides at the top, and set back by about 15mm, so that it leaves enough space for the mechanics when the cover is in place.
Then construct the four switches. Make sure that the holes in them are big enough to allow free movement around a toothpick axle.
Next, make eight chutes, one for each side of the four switches. Note that the four right-hand chutes, which lead directly into the baskets, have different lengths. Glue the chutes to the back plane. The schematic on the back plane shows where everything goes.
Also, there are brackets which go above the chutes. These will hold the toothpicks, and they have to align exactly with the holes in the back plane. At the center and below the actual switch, insert a small square as a spacer, so that the switch has enough space to move.
Next, make the baskets. This is fairly easy:
Now comes the cover. The cover has three sides, at the top, left and right. The bottom is left open, so that the marble can fall through. Make sure that the holes for the toothpicks and for the switches are large enough and allow free movement.
You also have to attach an extension of the back plane at the bottom, so that you can glue the baskets into place:
Insert all switches, using toothpicks. Fixate each toothpick by pushing a little disk onto it from both sides, but don’t squeeze too much, or the switch will no longer move smoothly.
That’s it. Attaching the cover is a bit difficult, as you have to thread all four toothpicks through the holes. You have to be a bit patient and persistent here. Also, for safety I strongly suggest to shorten the toothpicks to the actually required length, using side cutters.
For a true point-to-point encryption, you might want to build two copies of the machine.
Also, since the alphabet tables are included, anybody building the same machine will be able to decrypt your encoded messages. If you want to be on the safe side, I suggest using your own tables. For that purpose, I provide this blank cover where you can pencil in your own tables:
 This work is licensed under a Creative Commons Attribution-NonCommercial-NoDerivatives 4.0 International License. For more details on what you can and cannot do with my work, see here.
This work is licensed under a Creative Commons Attribution-NonCommercial-NoDerivatives 4.0 International License. For more details on what you can and cannot do with my work, see here.

















Pingback: Kuriose Verschlüsselungsmaschinen, Folge 3: Die polyalphabetische Steampunk-Verschlüsselungsmaschine zum Selberfalten – Klausis Krypto Kolumne
My god, you are amazing!!! Wow!! Im shock, great!! {UuU}
Pingback: Cipher Machine Papercraft « PaperCraft - models made of Paper PaperCraft – models made of Paper